Innovative IT Hub 623449400 operates within a complex security landscape. The hub employs advanced encryption techniques and biometric authentication to safeguard sensitive data. Additionally, it integrates threat intelligence to proactively identify vulnerabilities. Employee training plays a critical role in enhancing awareness of potential risks. As emerging technologies challenge traditional security measures, it raises important questions about the future of cybersecurity practices at the hub. What innovations might redefine their approach next?
Understanding the Security Landscape at IT Hub 623449400
Navigating the security landscape at IT Hub 623449400 requires a comprehensive understanding of both the physical and digital threats that can compromise its integrity.
Security challenges necessitate rigorous risk assessment protocols to identify vulnerabilities. By evaluating potential threats—ranging from unauthorized access to cyberattacks—stakeholders can develop strategies that ensure both data protection and operational continuity, fostering an environment conducive to innovation and freedom.
Key Security Protocols Protecting Sensitive Information
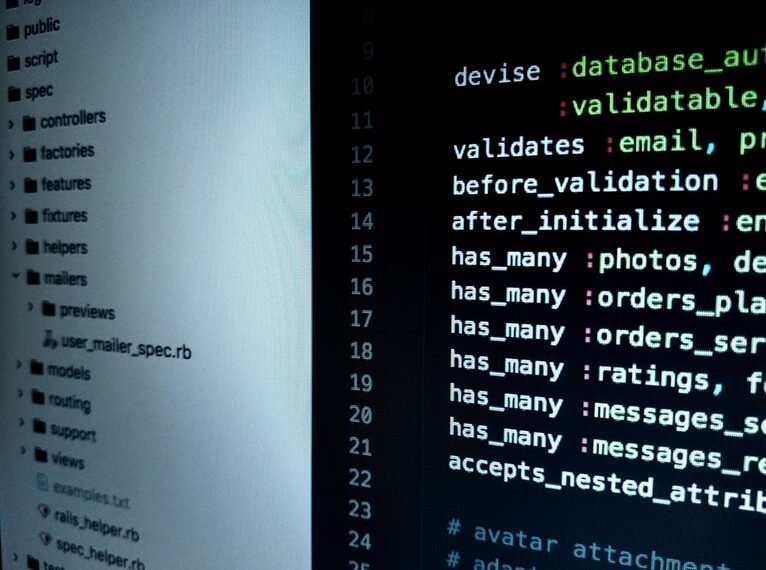
The protection of sensitive information at IT Hub 623449400 hinges on the implementation of robust security protocols designed to mitigate identified vulnerabilities.
Key measures include advanced encryption techniques, ensuring data confidentiality during transmission and storage.
Additionally, rigorous access controls restrict sensitive information to authorized personnel only, thereby minimizing the risk of data breaches and maintaining the integrity of critical systems and information.
Proactive Strategies for Mitigating Cyber Threats
Effective mitigation of cyber threats requires a multifaceted approach that integrates various proactive strategies.
Key components include leveraging threat intelligence to anticipate potential vulnerabilities and enhance security measures.
Additionally, comprehensive employee training programs foster a culture of vigilance, ensuring that personnel are equipped to recognize and respond to threats.
This dual focus empowers organizations, safeguarding sensitive data while promoting an environment of informed freedom and resilience.
The Future of Security: Innovations on the Horizon
Emerging innovations in security technology are poised to redefine the landscape of cyber defense.
Quantum encryption promises unbreakable data protection, leveraging the principles of quantum mechanics to secure communications against emerging threats.
Concurrently, biometric authentication enhances user verification through unique physiological traits, reducing reliance on traditional passwords.
Together, these advancements not only improve security but also empower individuals with greater control over their digital identities.
Conclusion
In a world where digital threats loom larger than ever, IT Hub 623449400 has mastered the art of security by embracing advanced technologies and training. Ironically, as they fortify defenses with cutting-edge encryption and biometric measures, one might wonder if the real challenge lies not in external threats, but in the human tendency to overlook the simplest vulnerabilities. Ultimately, their commitment to innovation may be both their greatest strength and their most ironic weakness in an ever-evolving cyber landscape.